Enterprise Journey Orchestration Platform
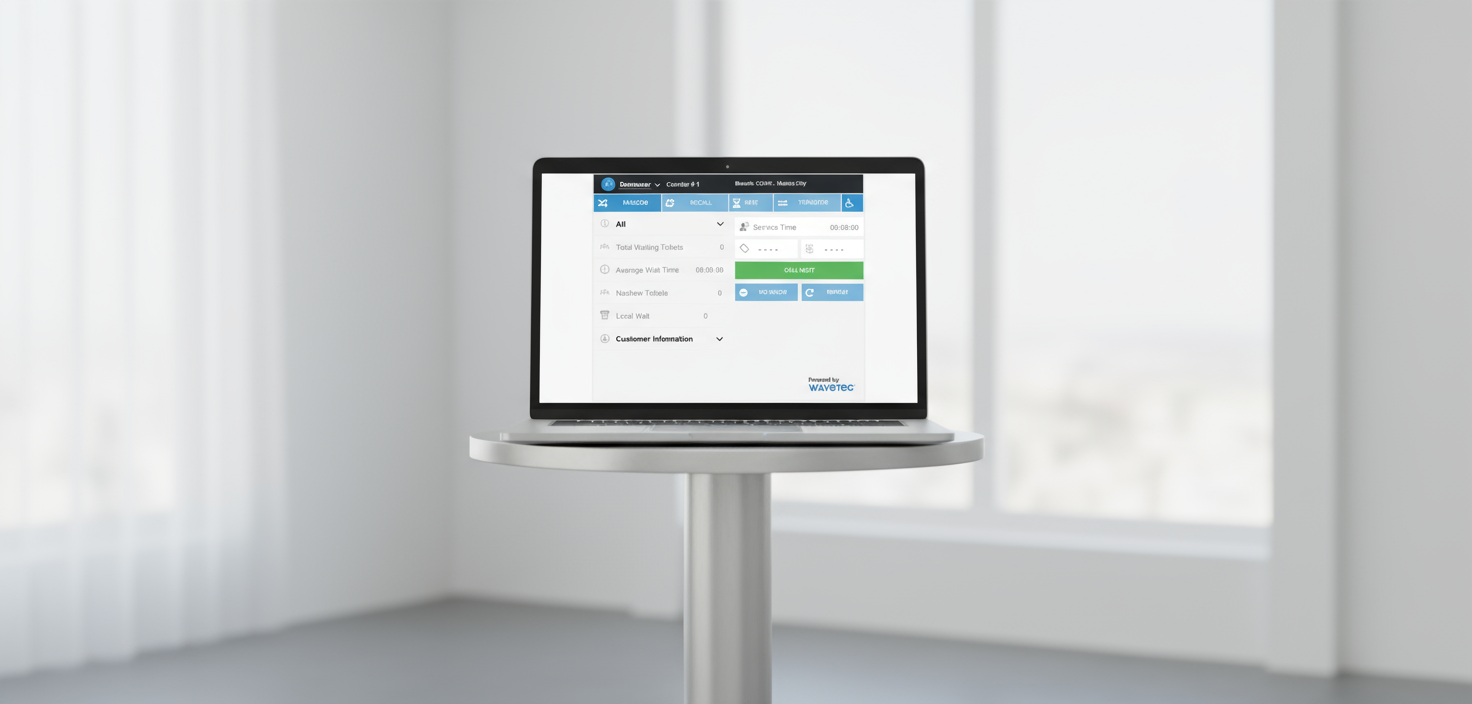
Spectra & ViOS is an enterprise platform for orchestrating customer flow across physical touchpoints—including kiosks, service counters, digital signage, guidance displays, and feedback points—and digital channels like the web, mobile apps, WhatsApp/messaging, and notifications. The problem modern enterprises face is that customers move across physical environments (branches, service centers, airports, retail stores, and government offices) and digital channels (mobile apps, WhatsApp, and web portals), but many organizations still operate these as separate systems. This fragmentation creates inconsistent journey logic across channels and locations, peak-time instability and operational firefighting, low self-service adoption due to reliability and trust concerns, fragmented monitoring with no unified view of touchpoints plus services and integrations, slow integration cycles with identity, core systems, and analytics platforms, and elevated security and privacy risks due to inconsistent access control, unclear retention rules, and limited auditability. Wavetec addresses this by centralizing orchestration logic and governance in a platform designed to be resilient, secure, integration-first, and operable at scale, providing a consistent control plane for policy execution, identity and access control, auditability, and operational observability with deployment flexibility across on-prem, hybrid, private cloud, and cloud-native environments.
Trusted by Leading Organizations


Enhancing Enterprise Journies
Orchestrating Customer Flow
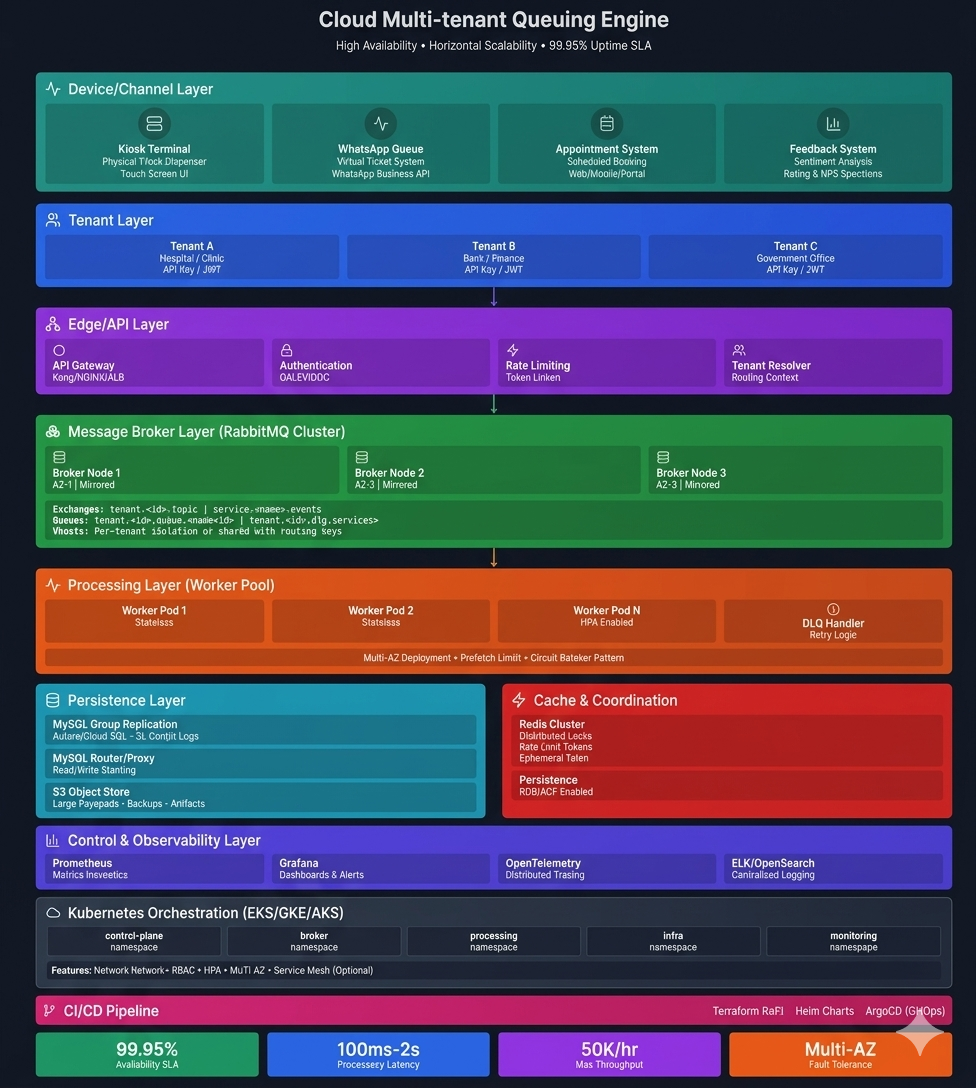
Wavetec’s platform is built on four core design priorities. First, the platform features a Policy engine with deterministic execution, providing central policy definition for routing, prioritization, segmentation, and SLAs to maintain consistent rules across all channels and locations. This system ensures controlled configuration and change traceability that is completely audit-ready, allowing for no downtime while changing configurations. Second, it guarantees High availability and failure isolation by designing services for redundancy through horizontal scaling and stateless architecture where possible. This ensures strict fault containment so single failures do not cascade into broad outages, while supporting controlled rollouts and rollbacks across multi-site environments and utilizing Kubernetes orchestration to provide self-healing and automated deployments. Third, the platform is Integration-first (transactional + event-driven), employing versioned REST APIs for synchronous actions and webhooks/events for near-real-time state propagation and workflow automation. It offers optional low-latency patterns like HTTP/2 and gRPC for edge-to-core use cases, ensures backward-compatible evolution with controlled deprecation practices, and delivers total integration flexibility to align with customer enterprise standards—including customer-selected API gateways, middleware, and data platforms. Finally, it establishes Security and privacy as baseline controls by supporting SSO (SAML/OIDC), RBAC, and strict separation of duties. This includes fully auditable administrative actions and security-relevant events, encryption in transit (TLS), configurable retention, and precise export controls, all resting on SIEM-friendly logging patterns and incident workflow hooks that offer out-of-the-box integration with SIEM solutions.
Enterprise Scale Deployments
Our platform is proven at scale, supporting massive infrastructure demands including Banorte with 1,200 branches operating in parallel, du with 280+ kiosks supporting millions of transactions, and Serco (Canada) across 90 locations.

Infrastructure & Core Execution
Edge device OS support: Windows, Linux, Android. Container orchestration: Kubernetes / Red Hat OpenShift (supported where required)/ Amazon EKS, Azure AKS. Core runtime: : JAVA /springboot/ .NET / NODE.JS /. CI/CD & artifact management: : AZURE DEVOPS / GITLAB CI / GITHUB ACTIONS / QUAY /.

Data, Messaging & Integration
API gateway: : KONG / NGINX / APIGEE / AZURE API MANAGEMENT / AWS API GATEWAY/Envoy. Messaging/eventing: : / RABBITMQ / / AWS SNS/SQS/MQTT (note: we have implemented eventing and queue-based integrations using customer-preferred middleware in past deployments). Primary database layer: : POSTGRESQL / MYSQL / MS SQL SERVER with HA patterns where applicable (note: we have supported enterprise database requirements as needed, including ORACLE in customer environments via custom integration and/or customer-managed data layers where required). Caching (optional): : REDIS.

Security, Identity & Operations
Architecture Overview (Edge-to-Core)
Edge Layer (What Users Interact With)
This layer handles endpoint experiences like kiosks, signage endpoints/controllers, and feedback capture points. It covers local device/peripheral control services where applicable, local resilience patterns for constrained networks where required, and supports operating systems including Windows / Linux / Android. The local data/cache layer, if used, supports: : SQLITE / MYSQL / LOCAL FILE STORE / OTHER.
Integration Layer (Enterprise Connectivity)
This layer features the API gateway handling authn/authz, throttling, validation, and observability hooks. It manages webhooks and event distribution for state changes and operational events, alongside integration adapters/patterns depending on the customer environment. The gateway technology includes: : KONG / NGINX / APIGEE / AZURE API MANAGEMENT / AWS API GATEWAY/Envoy, while eventing/messaging uses: : / RABBITMQ / / AWS SNS/SQS, noting that we have implemented deployments that align to customer-selected middleware standards.
Data and Analytics Layer
This layer controls operational datastore(s) for state, reporting, and retention, as well as analytics pipelines for KPIs, forecasting, and anomaly detection signals, plus export patterns for BI / data lake integration. The primary database engine is: : POSTGRESQL / MYSQL / MS SQL SERVER, utilizing an HA approach like: : REPLICATION/CLUSTER STRATEGY—E.G., PATRONI (POSTGRES) / INNODB CLUSTER (MYSQL) / ALWAYS ON (MSSQL). Data export formats include: : ODATA / REST / CDC / SFTP EXTRACT / OTHER, and enterprise customization history shows that deployments have supported customer-specific data platform requirements, including ORACLE-based environments via custom integration and/or customer-managed databases where required.
Core Orchestration Layer (Policy + Governance)
This layer manages journey policy services covering routing, prioritization, segmentation, and SLA logic. It handles configuration and governance services regarding versioning and audit trails, as well as identity and access enforcement through SSO integration + RBAC. The core service runtime utilizes: : JAVA / Springboot/ .NET / NODE.JS, while service-to-service communication relies on: : REST / GRPC / SOAP / GraphQL/ MIXED.
Observability Layer (Operations and NOC)
This layer monitors metrics, logs, and alerting, manages fleet health monitoring, and tracks dependency/integration health signals. For metrics/tracing it utilizes: : PROMETHEUS / OPENTELEMETRY / AWS Cloudwatch / OTHER, while the log pipeline runs on: : ELK/EFK / SPLUNK / SENTINEL / OTHER, and dashboards are powered by: : GRAFANA / KIBANA / OTHER / CISCO AppDynamics.
Deployment Models (Enterprise-Ready)
Deployment Models (Enterprise-Ready)
Wavetec supports multiple deployment models without changing the control plane principles. On-Prem setups offer customer-managed infrastructure and data residency, enterprise network zoning (DMZ/app/data tiers), and support LINUX / WINDOWS for servers using registries like QUAY / HARBOR / ARTIFACTORY / NEXUS. Hybrid models provide edge/local components where needed with centralized governance and analytics under customer controls. Private Cloud / Cloud-Native leverages container-based deployments for scalability and consistent release management with multi-zone/multi-node HA patterns. It relies on Kubernetes distributions like OPENSHIFT / UPSTREAM K8S / AKS / EKS / GKE, utilizing OPENSHIFT ROUTES / NGINX INGRESS / ISTIO GATEWAY for ingress and ISTIO / LINKERD / NONE for optional service mesh. For environments with limited outbound connectivity, Restricted-Network / Offline-Ready Scenarios offer governed artifact promotion via private registries, controlled release paths, and operational readiness without continuous cloud dependency. Offline update mechanisms include SIGNED BUNDLES / PORTABLE REGISTRY SYNC / INTERNAL PACKAGE REPO.

Resilience, Redundancy, and Uptime
Our typical high availability (HA) design approach centers on redundant service instances placed behind load balancing, with stateless services scaled horizontally where applicable. Database HA options use clustered designs and controlled failover patterns. The platform utilizes health checks, circuit breaking patterns where applicable, and retry/backoff guidance to prevent thundering herds during partial outages. Operational safeguards involve staged rollout, rollback, and config versioning, with backups handled via SNAPSHOT + PITR / SCHEDULED BACKUPS / OTHER. For disaster recovery (DR), we support ACTIVE-ACTIVE / ACTIVE-PASSIVE setups with tested restoration procedures where contracted.
Integration & Developer Experience
We support a wide array of integration patterns including REST/JSON APIs (OpenAPI/Swagger documented), webhooks for event-driven state propagation and workflow automation, decoupled event-driven workflows for reliability, HTTP/2 or gRPC for low-latency edge-to-core patterns where needed, and Batch/SFTP for controlled sync in legacy environments. Our Integration Pack provides OpenAPI/Swagger specifications, a webhook catalog (event types, schemas, signing guidance), and an event catalog (topics, schema evolution, retry semantics). It maps reference flows covering appointment → arrival → service progression → completion → feedback and offers sandbox options for integration testing where available. Supported SDKs include JAVA / .NET / JAVASCRIPT / PYTHON, while authentication options feature OAUTH2 CLIENT CREDENTIALS / JWT / MTLS / OTHER. To maintain stability, typical Enterprise Integration Controls include signed webhooks (HMAC) + replay protection guidance, idempotency guidance for event consumers, versioned APIs + controlled deprecation, rate limiting and backoff guidance, and structured error semantics for predictable integration behavior.

Operability and Monitoring (NOC-Ready)
Wavetec supports exactly what operations teams can run reliably. For Platform Observability, we track service health (latency, error rates, saturation, uptime), integration health (dependency latency/errors and endpoint availability), and SLA risk indicators with trend-based alerting, supported by APM/tracing via OPENTELEMETRY / JAEGER / ELASTIC APM / OTHER. Edge Fleet Monitoring tracks endpoint heartbeat/availability, device/peripheral status, and degradation detection over time for predictive maintenance patterns via MDM/EMM INTEGRATION / INTERNAL TOOLING / OTHER. Operational Integrations route alerts into ITSM/SOC workflows, using SIEM-friendly logging export/forwarding patterns and audit-ready traceability for administrative actions. We integrate with ITSMs like SERVICENOW / JSM / OTHER and SIEMs including SPLUNK / SENTINEL / QRADAR / OTHER. Release Governance covers staging → production promotion, ring-based rollout (pilot → controlled expansion), rollback strategy and configuration versioning, and maintenance windows and change control support operating on CI/CD tools like AZURE DEVOPS / GITLAB CI / ARGO CD / OTHER.
Security, Privacy, and Compliance (Trust Center)
Our baseline security controls feature SSO via SAML 2.0 / OIDC and precise RBAC centered on least privilege and separation of duties. Transport security relies on TLS for edge-to-core and service-to-service traffic, with audit logging monitoring administrative actions and critical configuration changes. Data governance policies enforce retention controls, access controls, and export controls with the scope defined per deployment. Operational security is maintained via secure configuration, governed deployments, and evidence readiness. Encryption at rest (where applicable) utilizes TDE / DISK ENCRYPTION / KMS-MANAGED KEYS, while secrets management is handled via KUBERNETES SECRETS / VAULT / CLOUD KMS.

Architecture, network zoning, SSO/RBAC, integration patterns, deployment options, and observability.


Frequently Asked Questions
Everything you need to know about the solution.
Yes. Deployments support on-prem, hybrid, private cloud, and cloud-native models. Architecture aligns with enterprise network zoning, data residency, and security control requirements without altering core governance principles.
The platform integrates with enterprise identity providers using SAML 2.0 or OIDC. Role-based access control, separation of duties, encryption in transit, and auditable logs support secure operational governance.
Both. REST APIs handle transactional actions, while webhooks and event-driven workflows propagate state changes in near-real time. Versioning and deprecation controls ensure backward compatibility.
Horizontal scaling, redundancy, health checks, and controlled rollout strategies protect uptime. Observability tooling provides SLA indicators and proactive alerting for rapid incident response.
A Trust Pack is available under NDA, including security documentation, governance summaries, and evidence artifacts relevant to enterprise procurement and compliance assessments.

Still have questions?
Can’t find the answer you’re looking for? Please chat to our friendly team.
